A Solution Unlike Any Other. Period.
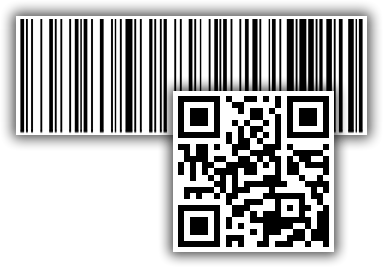
It is no surprise to us that businesses are plagued with rampant counterfeiting problems. We have yet to see a complete solution ourselves – that is why we devised Identifide. Here are just a few of the elements we have seen in other solutions which don’t quite make sense to us, and how we differ from them.